Resource Profile:
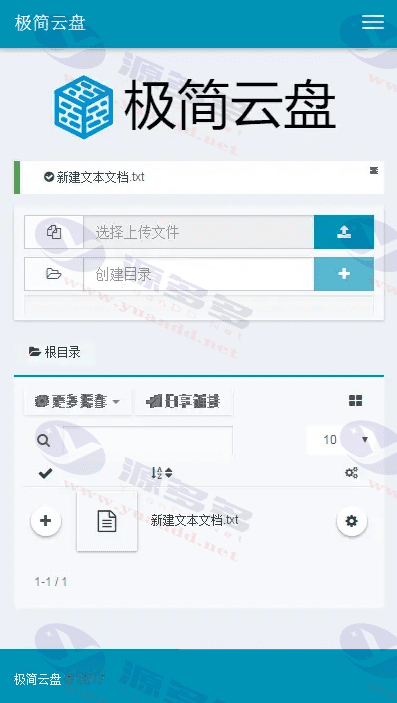
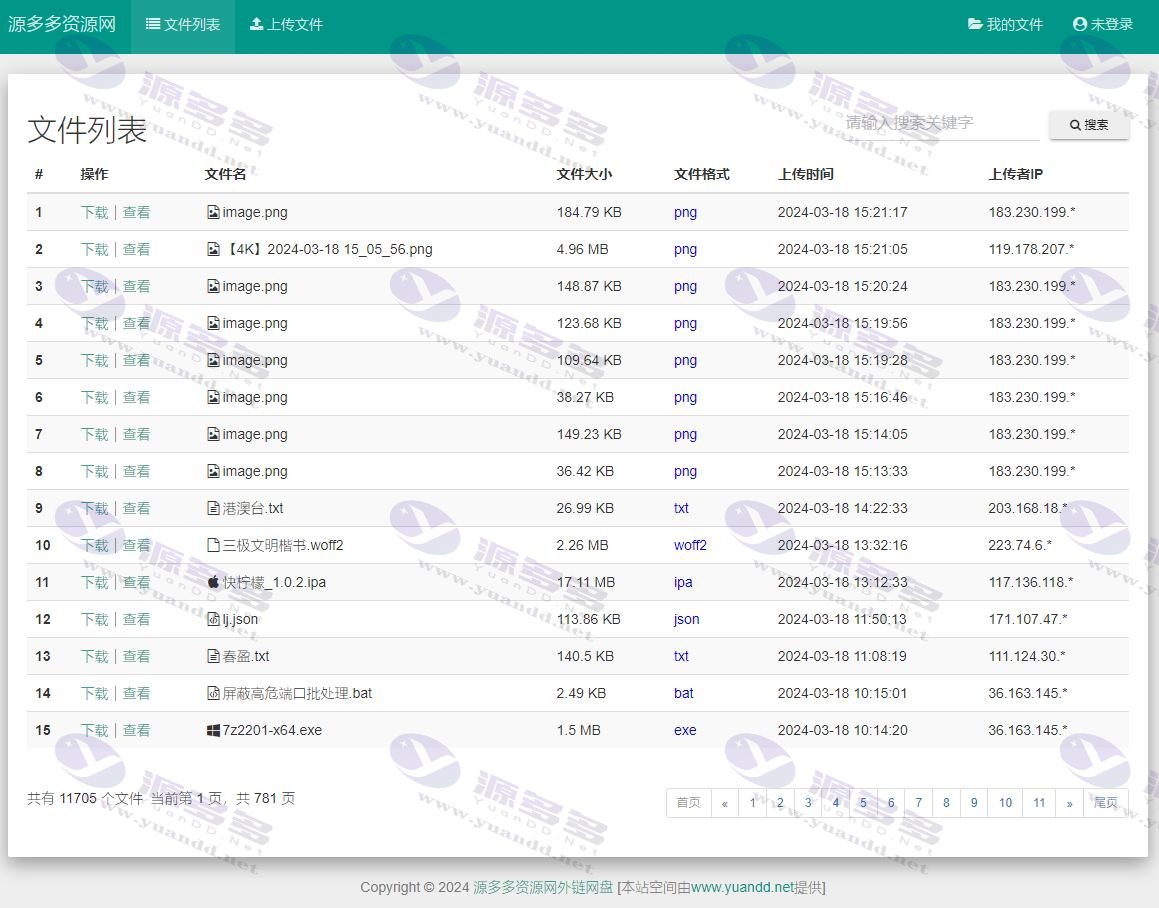
This is a set of Chinese optimized Veno File Manager-basedMinimalist Web DiskThe source code of the system, written in pure PHP, does not rely on a database, and is suitable for quickly building your ownpersonal cloud driveService platform. The system supports basic user registration, file uploading, generating sharing links, setting access passwords and other practical functions, lightweight and efficient, easy to deploy.
Upload the source code to a PHP-enabled server environment and you can use it directly without complicated configuration, especially suitable for private cloud disk applications with low resource consumption requirements.
It is recommended that you install it in an Apache environment and make sure that the .htaccess file works.
The program is ideal for a variety of scenarios such as personal file storage, private backups, and data sharing, making it an ideal lightweight web solution.
Photo Gallery:
- Can free downloads or VIP member-only resources be commercialized directly?
- The resources on this site are collected and organized through the network, for personal research and study purposes only. The copyright belongs to the legal owner of the software and program code, users should verify the copyright and legality of the resources, prohibited for commercial use, illegal activities or any violation of national laws and regulations.
- Disclaimer of liability for program or code bugs, compatibility issues or functional defects, etc.
- As the resources on this site are collected and organized through the network, not the site's original, it can not fully guarantee its functionality or code compatibility. Users need to verify whether the resources meet the needs of their own, due to the following circumstances lead to losses, this site does not assume any responsibility:
Programs, source code and other computer software resources may contain code vulnerabilities (bugs), compatibility issues or functional defects left by the developer. This site does not provide free repair services for such technical defects, users need to bear the risk of debugging, modification or abandonment of the use.