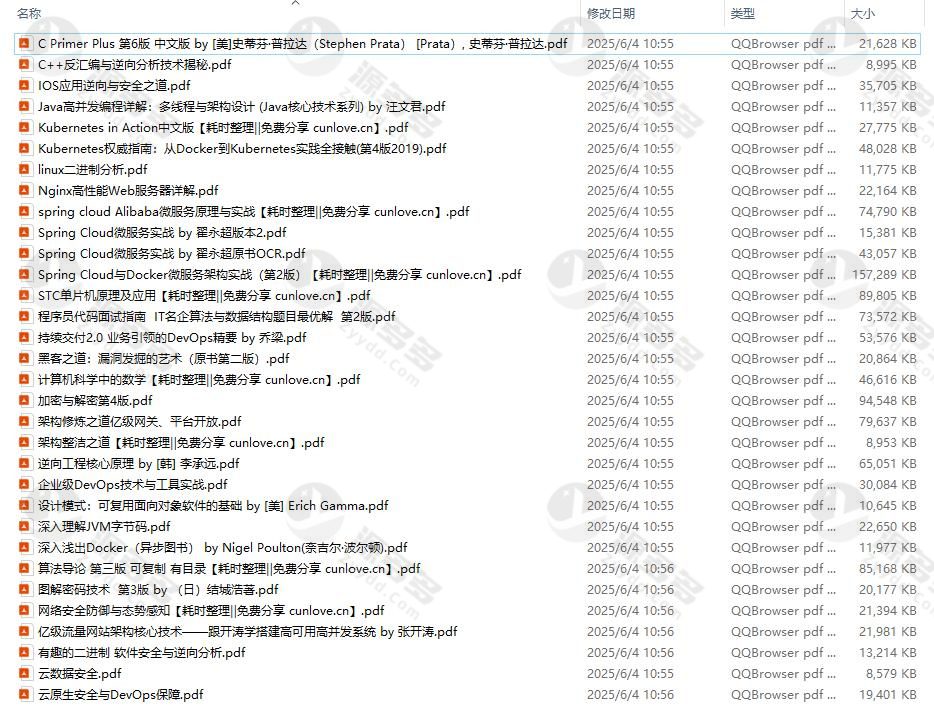
Resource Profile:
A selection of 34 high quality IT class technical eBook resources, covering programming and development, system operation and maintenance, reverse analysis, security architecture and other areas, suitable for programmers and network administrators as a learning and reference materials, only for technical research and personal study, not for commercial use.
A partial list of books included is below:
《C Primer Plus 第6版 中文版》作者:[美] Stephen Prata
C++ Disassembly and Reverse Analysis Techniques Revealed.
The Practice of Reversing and Securing iOS Applications.
Java Highly Concurrent Programming Explained: Multithreading and Architectural Design
Kubernetes Practical Guide (Chinese Edition)
The Definitive Guide to Kubernetes, Fourth Edition.
Introduction to Linux Binary Analysis.
Nginx High-Performance Web Services Explained.
Spring Cloud Alibaba Microservices in Action.
Spring Cloud Microservices in Action (OCR and PDF versions)
Spring Cloud and Docker Microservices Architecture in Action, Second Edition
Principles of STC Microcontrollers and Project Applications.
The Programmer's Interview Guide: Algorithms and Data Structures in a Nutshell, 2nd Edition.
Continuous Delivery 2.0: Core Essentials of Business-Driven DevOps
The Way of the Hacker: The Art of Vulnerability Mining (Second Edition)
Principles of Mathematics in Computer Science
Encryption and Decryption, Fourth Edition
The Tao of Architecture: Platform Openness and Gateway Design
The Tao of Architectural Neatness
Core Principles of Reverse Engineering
The Hands-On Handbook of Enterprise DevOps
Design Patterns: Fundamentals of Reusable Object-Oriented Software Development
A Deeper Understanding of the JVM Bytecode Mechanisms.
Docker in Depth.
Introduction to Algorithms, Third Edition with Catalog Reproducible Edition
Illustrated Cryptography, 3rd Edition
Cybersecurity Defense and Situational Awareness in Action
High Concurrency Architecture Core Technology: Billion Traffic System Design in Practice
Principles of Binary Software Security and Reversal
Cloud Data Security Fundamentals Tutorial
Cloud Native Security and DevOps Assurance Mechanisms.
The above materials are systematic technical books, suitable for developers and operation and maintenance engineers with a certain foundation to improve their skills. It takes a long time to organize the sources, so we recommend interested users to study and use them. Once again, please limit your use to personal study and technical research.
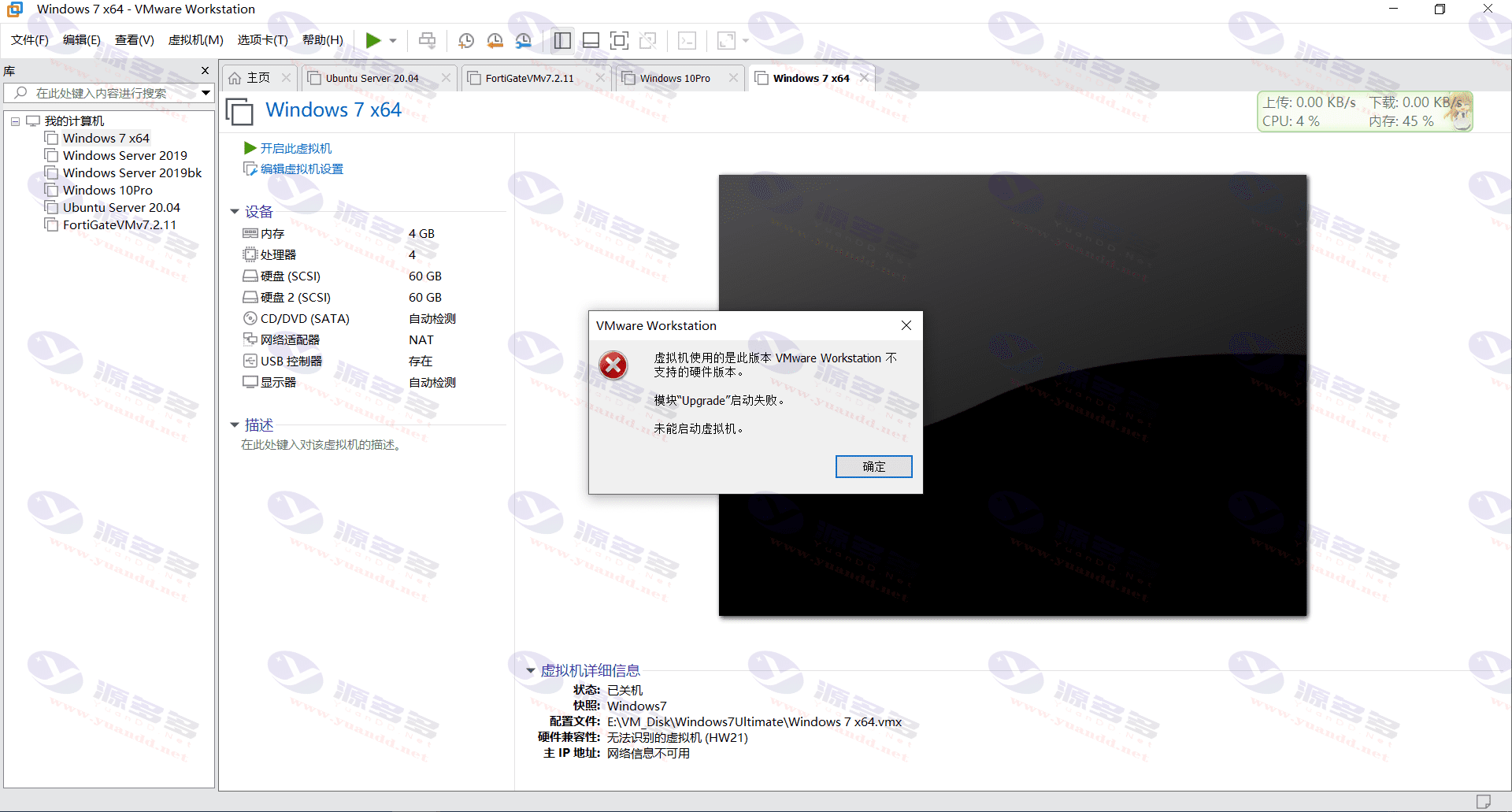
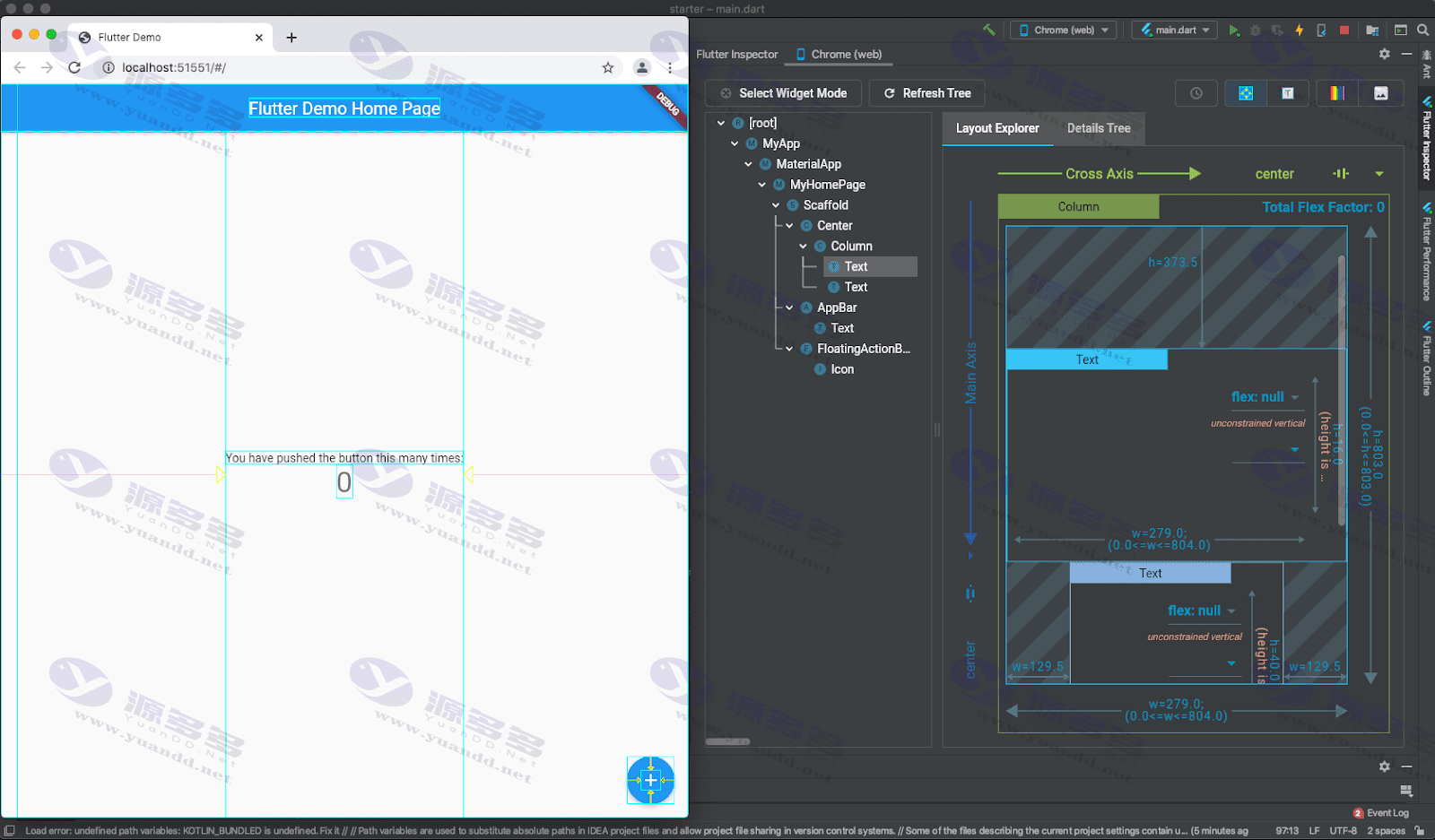
Photo Gallery:
- Can free downloads or VIP member-only resources be commercialized directly?
- The resources on this site are collected and organized through the network, for personal research and study purposes only. The copyright belongs to the legal owner of the software and program code, users should verify the copyright and legality of the resources, prohibited for commercial use, illegal activities or any violation of national laws and regulations.
- Disclaimer of liability for program or code bugs, compatibility issues or functional defects, etc.
- As the resources on this site are collected and organized through the network, not the site's original, it can not fully guarantee its functionality or code compatibility. Users need to verify whether the resources meet the needs of their own, due to the following circumstances lead to losses, this site does not assume any responsibility:
Programs, source code and other computer software resources may contain code vulnerabilities (bugs), compatibility issues or functional defects left by the developer. This site does not provide free repair services for such technical defects, users need to bear the risk of debugging, modification or abandonment of the use.